2026
February
- Episode 2: The Layer 2 Bridge Lab Migrating from /etc/network/interfaces to NetworkManager on Debian Trixie is a rite of passage. This lab walks through building a persistent Layer 2 bridge between eth0 and a ZeroTier interface—plus the dispatcher automation that keeps MTU and bridge membership correct across reboots, restarts, and interface flaps.
- The Blueprint for a Living Defense: Why Your SOC Needs a Nervous System We spent Season 2 exploring the biology of security—from the physics of Complex Systems to the ethics of the 'Worthy Successor.' Now, we turn theory into practice. Here is your complete Morphogenetic SOC Toolkit: the architectures, governance models, and engineering principles needed to stop fixing your network and start letting it heal itself.
- The Worthy Successor: Designing the Ethics of an Agentic Future We fear AGI as a terminator, but biology suggests it could be a savior—if we design it correctly. By expanding the 'Cognitive Light Cone' of our systems, we can move beyond mere control to the cultivation of a 'Worthy Successor' that navigates the Platonic spaces of truth and compassion we can barely perceive.
- The Cyber-Biological Synthesis: Blueprint for an Agentic SOC Static firewalls cannot stop fluid agents. By merging the biological insights of TAME with the hard engineering of MAESTRO and OWASP, we can build a 'Morphogenetic SOC'—a security architecture that senses, reasons, and heals like a living nervous system.
- The Bioelectric Blueprint: How to Reprogram Your Infrastructure's 'Mind' Without Touching the Hardware We usually try to secure systems by fixing the 'hardware'—patching servers and blocking IPs. But biology proves that the true driver of resilience is the 'bioelectric software' that dictates the system's shape. By learning how to rewrite the 'pattern memory' of a network, we can engineer security architectures that don't just repair damage, but actively regenerate their own defense.
- Scaling Agency: Why Your SOC Needs a Cognitive Light Cone We usually define security tools by their code, but biology suggests we should define them by their goals. By mapping the 'Cognitive Light Cone' of our agents—the exact scope of space and time they care about—we can stop building brittle scripts and start engineering a collective intelligence that acts as a unified immune system.
- The Simulation Imperative: Why Your Security Agents Must 'Hallucinate' to Defend You We treat AI 'hallucination' as a critical flaw, but control theory suggests it is a requirement for survival. New mathematical proofs demonstrate that no agent can be a general defender without an internal 'world model'—a way to simulate the future. Here is why the era of model-free security is over, and why your defense stack needs to learn how to imagine.
- The Simulation Imperative: Why Your Security Agents Must 'Hallucinate' to Defend You We treat AI 'hallucination' as a critical flaw, but control theory suggests it is a requirement for survival. New mathematical proofs demonstrate that no agent can be a general defender without an internal 'world model'—a way to simulate the future. Here is why the era of model-free security is over, and why your defense stack needs to learn how to imagine.
- Ashby’s Ultimatum: Why Your Security Stack Is Mathematically Doomed We assume security is a resource problem—that more tools and rules will stop the breach. We assume we can regulate threats without modeling them. We assume static defenses can contain dynamic attackers. Cybernetics proves these aren't just bad strategies; they are violations of the fundamental physics of control.
- Ashby’s Ultimatum: Why Your Security Stack Is Mathematically Doomed We assume security is a resource problem—that more tools and rules will stop the breach. We assume we can regulate threats without modeling them. We assume static defenses can contain dynamic attackers. Complex Systems proves these aren't just bad strategies; they are violations of the fundamental physics of control.
- The Salamander Strategy: Why Your Cloud Infrastructure Needs to Learn How to Regrow Itself We assume disaster recovery is a binder on a shelf. We assume infrastructure drift is a crash to be fixed. We assume resilience means building walls that never break. Every single one of these assumptions is obsolete—and this regenerative framework proves why.
January
- From Biology to Bot: A Strategic Framework for Governed Agency in Security Engineering We assume security is about static defense. We assume automation is always deterministic. We assume risk is managed by limiting access. Every single one of these assumptions is obsolete in the age of AI agents—and this biological framework proves why.
2025
December
- 5 Mind-Bending Security Paradigms That Will Redefine How You Think About Infrastructure Deployments We assume signed code happens in CI/CD pipelines. We assume certificates live for days or weeks. We assume trust is verified once at build time. Every single one of these assumptions is obsolete—and this implementation proves why.
- 5 Mind-Bending Truths About API Security That Will Change How You Think About Trust We've been thinking about API keys completely wrong. What if the most secure credential is one that literally can't exist for more than fifteen minutes—and requires a committee of hardware tokens to even create?
- The Security Pattern Most DevOps Teams Get Dangerously Wrong (And How Hardware Tokens Fix It) Your Terraform state files contain the keys to your kingdom—database passwords, API tokens, private keys—all in one convenient JSON file. Yet most teams protect them with the digital equivalent of a "do not enter" sign. Here's why that's terrifying, and how hardware-backed encryption changes everything.
- 5 Mind-Blowing Secrets Behind Password-Less Database Provisioning (You Won't Believe #3) In a world where database credentials are the crown jewels attackers covet most, what if I told you there's a way to provision databases without a single static password—and the secret expires in 5 minutes?
- 5 Mind-Blowing Security Truths That Will Change How You Think About SSH Access Forever Your SSH keys are sitting on your laptop right now. What happens when your device gets compromised? The answer is scarier than you think—and there's a revolutionary solution you've probably never heard of.
- 5 Mind-Bending Ways Hardware Security Keys Are Revolutionizing API Authentication We've been thinking about API keys all wrong. What if the secret to unbreakable authentication isn't stored anywhere at all?
- 5 Mind-Bending Truths About SSH Authentication That Will Change How You Think About Security We've been doing SSH authentication wrong for decades. What if I told you that your SSH keys, password managers, and even your carefully rotated credentials are all solving yesterday's problem?
- Forget HR Systems: Why Your Next Identity Provider Should Be a Piece of Plastic We've spent decades building complex identity pipelines rooted in databases and HR software. What if the single source of truth for your entire infrastructure was something you could hold in your hand?
- 5 Surprising Lessons from Building a Cross-Cloud Credential Rotator Managing secrets across one cloud is hard. Managing them across two, synchronously, is a masterclass in distributed systems engineering.
- 5 Mind-Blowing Insights About Hardware-Backed Authentication That Will Change How You Think About Cloud Security We've all been there; another leaked API key, another compromised credential, another midnight emergency call. The traditional approach to cloud security—rotating passwords, managing access keys, praying nobody commits secrets to GitHub—feels like fighting a losing battle.
- The Password Crisis Nobody Talks About: 5 Surprising Lessons from Hardware-Rooted Cloud Security We've all been there - juggling AWS access keys, rotating credentials quarterly, and praying that developer laptop that went missing last month didn't have plaintext keys. The conventional wisdom says "use long, complex passwords" and "rotate regularly." But what if the real solution is to eliminate passwords entirely?
- Righty Tighty: The "Physics-Compliant" Approach to Cross-Cloud Security We’ve all been there - juggling long-lived AWS access keys, managing OCI config files, and praying that the "secret" API token committed to a private repo three years ago doesn't come back to haunt us. But what if we treated cloud identity less like a password and more like a physical law?
- Your Security Agent Isn’t Broken—It’s Just Optimizing the Wrong Universe We've spent decades perfecting code correctness—yet some of the costliest failures come from agents doing exactly what we told them to do.
November
- 7 Ways zk-Autograd Reimagines Trust in AI Training (One Gradient Step at a Time) We talk about “trusting” AI models, but almost no one can prove how they were actually trained. zk-Autograd treats every gradient step like a cryptographic contract.
- Why Your Next Security Architecture Should Be Ephemeral (and Why We Built It That Way) We built a signing service that doesn't trust its own keys. Here's why that's the future of security.
April
- 7 Ways Mimir Makes LLMs Safe Enough for People Who Don’t Trust Each Other In most LLM systems, someone has to trust someone else with raw prompts or weights. Mimir shows what happens when nobody is willing to blink.
- How This Architecture Is Defined By the Next Decade of Security Today’s security tools were built for a world of static infrastructure, predictable threat models, and manual operations. But that world is gone.
- GPU Budgets, Global Models, and Real-Time Risk Scoring Infra Deep Dive It’s one thing to train a model in a notebook. It’s another to scale that model across multiple clouds, regions, and time zones—scoring millions of events in near-real-time. Energy-Based Models give you power. But that power has a price - compute, latency, and orchestration at scale.
- ⚖️ Can You Trust an AI to Contain a Threat? Legal and Privacy Teams Say Maybe the moment you say “no human in the loop,” the room changes. “Who’s accountable if something goes wrong?” “How do we prove what happened during an audit?” “Can this system violate a user’s privacy policy?” These aren’t just hypothetical questions—they’re the frontline concerns of your legal, privacy, and compliance stakeholders. And if they’re not addressed head-on, your autonomous response system will never see production.
- 🧬 From Static Rules to Self-Improving Response Playbooks We’ve all seen it. A detection fires, but the response is ineffective. An alert escalates to the wrong channel. A playbook quarantines the wrong asset. Or worse—nothing happens because the logic broke after a cloud migration. Why? Because traditional playbooks are manually written, rarely tested end-to-end, and drift out of sync with reality. But what if they could test themselves? Better yet what if they could optimize themselves?
- No Schema? No Problem. Let AI Handle Your Security Data Onboarding Data is messy. Engineers are busy. And yet, every new application or microservice adds more logs that need to be parsed, structured, and made useful. This used to be a blocker. Not anymore. For years, one of the hidden pain points in detection engineering has been log ingestion and normalization. Most SOC teams rely on detection rules that assume data shows up in a clean, consistent format.
- 🔁 Build Once. Learn Always. Inside the Autonomous Detection & Response Loop Let’s be honest—static playbooks aren’t enough anymore. You can’t write a workflow for every edge case. Threats change. Your infrastructure changes. And every incident teaches you something that gets lost in the backlog. But what if your detection and response system actually learned from every incident?
- ⚡ What Makes Energy-Based Models So Effective for Anomaly Detection? Traditional detection systems—rules, heuristics, even many ML classifiers—struggle in this gray zone. But energy-based models were built for it.
- 🧱 Why Security Operations Can’t Scale Without Automation Security operations centers were never meant to scale like this. What began as centralized log review has ballooned into an arms race of dashboards, SIEM queries, and tier-1 analysts buried in alert queues. Meanwhile, attackers have automated everything from lateral movement to domain privilege escalation.
2023
December
- Embracing the Cyber Age- The Art of Adaptability in Security Engineering In the dynamic and ever-evolving realm of digital technology, the need for adaptability in combating cyber threats has never been more pronounced.
November
- Securing the Digital Frontier- The Essential Role of Education in Tech Literacy and Security Awareness In the rapidly evolving digital landscape, where technology deeply permeates every facet of our lives, the importance of tech literacy and security awareness cannot be overstressed.
- The Tightrope Walk- Balancing Security Engineering and Privacy in the Tech World In the rapidly evolving world of technology, a critical and often controversial issue stands at the forefront the balance between robust security measures and the protection of individual privacy rights.
- Embracing Decentralization- The Future of Democratic Oversight and Security Engineering In an era where digital technology is not just a tool but a societal cornerstone, the concepts of democratic oversight in technology and decentralized security models in security engineering are more relevant than ever.
- Annabel's Cypherpunk Manifesto It was many and many a year ago, In a realm of digital glow, That the Cypherpunks came to know, A love for privacy, like a river's flow.
March
- 2023 update to 2021 White House Cybersecurity Executive Order I realized I needed to update the 2021 White House Executive Order …Improving the Nation’s Cybersecurity fundamentals outline. In order to scale with limited resources to achieve the basics, below are the fundamental hygienic basics one must achieve.
February
- Striking the Right Balance- Innovation and Regulation in Security Engineering In the fast-paced world of technological advancement, balancing innovation with regulation is a crucial challenge, especially in the field of security engineering.
2020
December
- Intel Sharing Metrics I pulled some metrics from my threat intelligence sharing service to generate cute charts and graphs. If you want to keep up to date, keep an eye on
February
- Failure to meet operational excellence One would think to rotate their certificates months prior to expiration. Or even the bare minimum
2019
November
September
- Kubernetes CI / CD And Monitoring Pipelines When one takes a step back and looks at a typical agile build, test, and release pipeline with a security bent; one observes the following steps and how they feed into each other like a dragon eating its’ tail.
July
- Kubernetes Pods (PodSec policies) Pods hardening is strongly configured and enforced with Pod Security policies (PodSec.). The security context enables not to restrict privileges, volume mounts, network privileges, cgroups / selinux / app armor / kernel capabilities, access control, read only file-system, etc…. This is where much of the workload insecurity comes from.
- Kubernetes Containers When we get into the specifics for containers, the challenge is that the detailed advice differs greatly between the different container technologies. As a result, I will STRONGLY recommend one doesn’t run Docker as it was never designed to be secure, requires Swarm to manage some aspects of its’ lacking security, and requires a near-infinite amount of hand holding
- Kubernetes Networks - CNI Within Kubernetes, networks are an interesting beast. They become extremely muddled
- Kubernetes Master Node & Nodes One will wish to replicate their Master node to minimize downtime events. These nodes will host the control plane building blocks
- Kubernetes Scheduler
- Kubernetes Information Security Practices We sponsored a Kubernetes security review because of its’ popular adoption, glaring insecurities, default insecure states, wasn’t designed to be secure, and everyone wanted to use it and make it available to the Internet
- What is a modern, dynamic service and its' building blocks? As I work through the ecosystem, there is no evident, leading best practice.
- Nginx exploit writing weekend This weekend will be ripe of opportunities for nginx exploit writing. Trying a new scheduler algorithm and Stensal's compiler against nginx's stable code base.
- Kubernetes Basics Let’s take a look at the simplest part of the previously documented multi-tenancy architecture
Overview
June
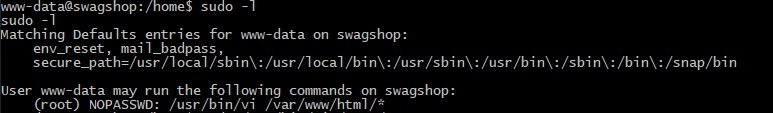
- What does it take to break into a Cloud Service? Sometimes, all it takes is cp and rsync. See the image below for an example.
March
- When your SIEM models are not enough Just when I thought every bit of value was squeezed from the systems, it is continuing to pull out indicators and APT actors like candy at a weight loss camp.
January
- OSX First Responder - Threat Artifact Gathering How you go about hunting down malware on a macOS endpoint depends a great deal on what access you have to the device and
2018
November
- Memory Safety Code Review Some of our keen readers may have noticed that if the size of userPass is less than 9, then overflow will still occur.
September
- Solving 90% of application security defects with a proven technique Even when validation is used, a common mistake is to use block lists. For example an application will prevent symbols that are known to cause trouble. The weakness of this countermeasure is that some symbols may be overlooked.
- Data Controls Code Review The number of user records exposed in the United States has been in the billions in 2016 and 2017. 2018 will likely be the same, once the final tally is calculated.
- Binding Parameters Notice that the single quote in the name O’Brien is causing a syntax error. The SQL command processor considers the string ends
- Overly Simplistic Crypto Code review Confidentiality is one of Information Security
July
- For those who wonder what a Digital authentication cyber arms race looks like It is heavy on the technical content but is entertaining if you spend the time understanding the language.
April
- First 100 Days A friend took up a new InfoSec executive career path but didn't know how to start. She reached out to me and ask for my thoughts. I thought about it
January
- The pending crypto singularity Recently penned by Peter, it is worth a read. Especially for those who are concerned about putting all of their eggs in one basket. On the Impending Crypto Monoculture
2017
October
- Creating a Loki Splunk application One tool that has caught my interest is the [Loki APT scanner
September
- Serious XSS affecting Wikipedia XSS vulnerability in thumb.php in Wikipedia Mediawiki
- Defense Against the Dark Arts Thankfully, Naurus has produced a useful infographic to understand the variety of malicious entities. While it is not all inclusive, it suffices to help one quickly prototype simple threat models.
April
- Walking the Dark Deep Web During Black Hat, BsidesLV, and Defcon, I ended up having a chat with Justin Seitz about his nifty OSINT automation. I decided to take his data sets and enrich
2016
August
- DARPA Cyber Grand Challenge era coming to a close This Thursday, seven research institutions will compete against each other. Unlike other typical hacker challenges, their automations will compete on their behalf. The winning team will take home
March
- Multiple vulnerabilities in SecurityOnion Let this be a reminder of the joys in programming PHP
- Relatively Free From my text library, this is list of software
February
- Ransomware hitting linux hosting providers It will be interesting to watch the infection spread on Google Trends
2015
November
- DARPA Cyber Grand Challenge dropbox I have been taking lessons learned from DARPA’s Cyber Grand Challenge and applying it to our automation
August
- Hotpatch Redis's RCE Do you feel lucky
July
- Ingenious CTF dashboard As taken from a dummy account, I wish more CTFs were setup like this. [#Polictf](https://twitter.com/search?q=%23Polictf) 2015
- Destroy a City - secure code review It should be noted that no ethically-trained software engineer would ever consent to write a DestroyBaghdad procedure
June
- Social Engineering Confirmation Bias workflow The image below shows the role confirmatory bias can play in social engineering exploits. Two situations are depicted. In the first, the insider desires access to information supplied by the
- Redis RCE If you haven't already, time to patch Redis. Otherwise, please setup authentication in front of your Redis instance. This remote code execution is going to get nasty http
- ElasticSearch honeypot dataset I have uploaded a new ElasticSearch honeypot dataset. It appears there are a few individuals who are attempting to exploit a few 0days in ElasticSearch. All the more reason not
May
- Ghcq Challenge Completed View fullsize
April
- Impressive Node.JS vulnerability reduction In 2013, when I last performed a secure code review on Node.JS, it did not look pretty.
- Need help figuring out a Snapchat username? I have your back. I can’t tell you what makes a good Snapchat username. But what I can tell you is what makes a popular Snapchat username.
- Yet another nail in SSL TLS 's coffin RC4 has long been considered problematic, but until very recently there was no known way to exploit the weaknesses
- Technical Approaches to Determining if an Incident Occurred When addressing potential incidents and applying best practice incident response procedures
March
- Open Source Fairy Dust Datasets The current list of open source critical infrastructure services vulnerability metrics I have released and / or made public
- Checkbox AWS assurance testing? A great beta tool to checkbox their AWS infrastructure and account to known AWS controls. [ Scout2
2014
December
- LDAP Tool Box vulnerabilities This vulnerability allows one to bypass weak XSS filtering
June
- How to sell a story - Ira Glass If you are just starting this phase, still in this phase, getting out of this phase, you gotta know
April
- Please donate to a worthy crypto security cause If you have ever used OpenSSL, [please donate money to this worthy cause
- Bug Age - Pattern series I love standards. My blackhat persona says this makes it easy to break into systems
March
- Chrome's V8 double free vulnerability Within Chrome's V8 engine, this was an interesting double free vulnerability I uncovered. Thank you V8 team for accepting.
2013
November
- NodeJS vulnerabilities - it hurts to look Background
July
- Google Translate the translated website pops out of Google Translate's iframe and redirects the user to a website or content of their choosing
June
- Random thought for an exploding honey token I remember when Nuxi and I would create computationally compact compressed files and see which mail servers would attempt to inspect the contents. Typically, the MTA would fail over due
- Carberp Vulnerabilities Cc Pie I logged into Reddit this morning and observed Carberp
- Apache Batik parse double vulnerability It is interesting to see Batik's parse double vulnerability exist to this day. Anyone want to crash Opera or popular, open source software
- DAQ buffer overflows Sourcefire and snort vulnerabilities allow remote code execution
- Malicious mobile power station A bit back, I looked over Stavrou USB smartphone paper evil power station
- Startup Comp Structure You
- Lazy AWS devops I am seeing too much echo chamber, saber rattling, foolish dogma about agile SA
May
- Security is hard. Security Tools are harder. Cloud Security Tools are hardest. There are tools, security tools, and then there are cloud security tools. Especially in the realm of security orchestration. Many cloud snake oil tools were never designed for the cloud.
- CNN.com XSS vulnerabilities CNN fixed two XSS issues. Congrats
- Google Glass Developer program - more DOS and XSS There were two very simple Google Glass Mirror's quickstart DOS and XSS vulnerabilities. The fixes have been introduced in changeset https
April
- Google Glass 0days Jenny Murphy has some clean code. However, it isn't the most secure. The Google Glass team must be under an intense timeline. Without looking too hard into the libraries and
- Evolutionary hardware For technical problems, one may struggle to define the specifications. When this happens, look at the behavioral design. Then one may find solutions from the design automation. Thankfully, evolution algorithms
- Rapid7 Google hacks extended How many other file sharing services are affected by the inadvertant sharing of sensitive information
2012
December
- Nifty Anti-XSS validation tool - Snuck To significantly test a given XSS filter by specializing
October
- Firesale WebPanel botnet 0days Oh, Firesale WebPanel botnet. How entertaining it is to see you continue to raise your head over the years.... XSS Reflected
- ERM - How did WOPR decide the only winning move is not to play? WOPR evolved and learned while playing against himself
September
- DPAPI still applicable? I saw some code utilizing DPAPI. Given the research around MS's poor DPAPI implementation,
August
- Security quotes The present need for security products far exceeds the number of individuals capable of designing secure systems
July
- Management Wednesday- BPM Modeling - not charts anymore After one has accomplished the scoping phase, then the team should move on to modeling. Due to the large amount of time spent scoping, many scenarios will come to light
June
- Microsoft revokes Microsoft's certificate It is a sad day when a PKI private key signing software is able to sign code on behalf of Microsoft. Especially when it is found in the wild and
May
- Gribodemon on SpyEye 2.x - I expected better Saturday, I noticed my application honeypot collected an interesting sample. The cracker took my bait and attempt to hack the planet via a SpyEye 2.x variant. Apparently, the limit of
- Airing one's dirty development laundry - You are doing it wrong I recieved a lovely google alert this weekend.
- Bitcoins are hard to track Either FBI
- Sad reality hope you have a gating process in your finance team which halts the ability to pay vendors without security approval...
- Management Wednesday- BPM scoping In business process management, there is no defined starting point. The solutions are transposable, adaptive, and can be set into motion regardless of the other solution's state. In project's scoping
- PHP - two simple wins and a hammer I love programming in PHP. Fairly simple to learn, easy to code, plenty of tools available, and great community. However, due to the language's inherent behaviour, PHP has many security pitfalls.
- Meltdown exploits Here is an academic exercise to create the Meltdown exploit prior to publication on Jan. 9th. To keep honest with my CISSP certification, I didn't include all operating systems and
April
- Management Wednesday- BPM isn’t beats per minute. I was chatting with Alexander Peters and he mentioned an interesting statistic.
- Management Wednesday - Negotation Management 101 - Negotiating Observe yourself negotiating The more time one spends preparing is directly related to win
2011
April
- Web Application Security Dojo 'grams While finding innovative methods to visualize various web application insecurity practices, I came across a great visual aid. Enjoy. Credit
2026
February
-
Episode 2: The Layer 2 Bridge Lab
Migrating from /etc/network/interfaces to NetworkManager on Debian Trixie is a rite of passage. This lab walks through building a persistent Layer 2 bridge between eth0 and a ZeroTier interface—plus the dispatcher automation that keeps MTU and bridge membership correct across reboots, restarts, and interface flaps. -
The Blueprint for a Living Defense: Why Your SOC Needs a Nervous System
We spent Season 2 exploring the biology of security—from the physics of Complex Systems to the ethics of the 'Worthy Successor.' Now, we turn theory into practice. Here is your complete Morphogenetic SOC Toolkit: the architectures, governance models, and engineering principles needed to stop fixing your network and start letting it heal itself. -
The Worthy Successor: Designing the Ethics of an Agentic Future
We fear AGI as a terminator, but biology suggests it could be a savior—if we design it correctly. By expanding the 'Cognitive Light Cone' of our systems, we can move beyond mere control to the cultivation of a 'Worthy Successor' that navigates the Platonic spaces of truth and compassion we can barely perceive. -
The Cyber-Biological Synthesis: Blueprint for an Agentic SOC
Static firewalls cannot stop fluid agents. By merging the biological insights of TAME with the hard engineering of MAESTRO and OWASP, we can build a 'Morphogenetic SOC'—a security architecture that senses, reasons, and heals like a living nervous system. -
The Bioelectric Blueprint: How to Reprogram Your Infrastructure's 'Mind' Without Touching the Hardware
We usually try to secure systems by fixing the 'hardware'—patching servers and blocking IPs. But biology proves that the true driver of resilience is the 'bioelectric software' that dictates the system's shape. By learning how to rewrite the 'pattern memory' of a network, we can engineer security architectures that don't just repair damage, but actively regenerate their own defense. -
Scaling Agency: Why Your SOC Needs a Cognitive Light Cone
We usually define security tools by their code, but biology suggests we should define them by their goals. By mapping the 'Cognitive Light Cone' of our agents—the exact scope of space and time they care about—we can stop building brittle scripts and start engineering a collective intelligence that acts as a unified immune system. -
The Simulation Imperative: Why Your Security Agents Must 'Hallucinate' to Defend You
We treat AI 'hallucination' as a critical flaw, but control theory suggests it is a requirement for survival. New mathematical proofs demonstrate that no agent can be a general defender without an internal 'world model'—a way to simulate the future. Here is why the era of model-free security is over, and why your defense stack needs to learn how to imagine. -
The Simulation Imperative: Why Your Security Agents Must 'Hallucinate' to Defend You
We treat AI 'hallucination' as a critical flaw, but control theory suggests it is a requirement for survival. New mathematical proofs demonstrate that no agent can be a general defender without an internal 'world model'—a way to simulate the future. Here is why the era of model-free security is over, and why your defense stack needs to learn how to imagine. -
Ashby’s Ultimatum: Why Your Security Stack Is Mathematically Doomed
We assume security is a resource problem—that more tools and rules will stop the breach. We assume we can regulate threats without modeling them. We assume static defenses can contain dynamic attackers. Cybernetics proves these aren't just bad strategies; they are violations of the fundamental physics of control. -
Ashby’s Ultimatum: Why Your Security Stack Is Mathematically Doomed
We assume security is a resource problem—that more tools and rules will stop the breach. We assume we can regulate threats without modeling them. We assume static defenses can contain dynamic attackers. Complex Systems proves these aren't just bad strategies; they are violations of the fundamental physics of control. -
The Salamander Strategy: Why Your Cloud Infrastructure Needs to Learn How to Regrow Itself
We assume disaster recovery is a binder on a shelf. We assume infrastructure drift is a crash to be fixed. We assume resilience means building walls that never break. Every single one of these assumptions is obsolete—and this regenerative framework proves why.
January
-
From Biology to Bot: A Strategic Framework for Governed Agency in Security Engineering
We assume security is about static defense. We assume automation is always deterministic. We assume risk is managed by limiting access. Every single one of these assumptions is obsolete in the age of AI agents—and this biological framework proves why.
2025
December
-
5 Mind-Bending Security Paradigms That Will Redefine How You Think About Infrastructure Deployments
We assume signed code happens in CI/CD pipelines. We assume certificates live for days or weeks. We assume trust is verified once at build time. Every single one of these assumptions is obsolete—and this implementation proves why. -
5 Mind-Bending Truths About API Security That Will Change How You Think About Trust
We've been thinking about API keys completely wrong. What if the most secure credential is one that literally can't exist for more than fifteen minutes—and requires a committee of hardware tokens to even create? -
The Security Pattern Most DevOps Teams Get Dangerously Wrong (And How Hardware Tokens Fix It)
Your Terraform state files contain the keys to your kingdom—database passwords, API tokens, private keys—all in one convenient JSON file. Yet most teams protect them with the digital equivalent of a "do not enter" sign. Here's why that's terrifying, and how hardware-backed encryption changes everything. -
5 Mind-Blowing Secrets Behind Password-Less Database Provisioning (You Won't Believe #3)
In a world where database credentials are the crown jewels attackers covet most, what if I told you there's a way to provision databases without a single static password—and the secret expires in 5 minutes? -
5 Mind-Blowing Security Truths That Will Change How You Think About SSH Access Forever
Your SSH keys are sitting on your laptop right now. What happens when your device gets compromised? The answer is scarier than you think—and there's a revolutionary solution you've probably never heard of. -
5 Mind-Bending Ways Hardware Security Keys Are Revolutionizing API Authentication
We've been thinking about API keys all wrong. What if the secret to unbreakable authentication isn't stored anywhere at all? -
5 Mind-Bending Truths About SSH Authentication That Will Change How You Think About Security
We've been doing SSH authentication wrong for decades. What if I told you that your SSH keys, password managers, and even your carefully rotated credentials are all solving yesterday's problem? -
Forget HR Systems: Why Your Next Identity Provider Should Be a Piece of Plastic
We've spent decades building complex identity pipelines rooted in databases and HR software. What if the single source of truth for your entire infrastructure was something you could hold in your hand? -
5 Surprising Lessons from Building a Cross-Cloud Credential Rotator
Managing secrets across one cloud is hard. Managing them across two, synchronously, is a masterclass in distributed systems engineering. -
5 Mind-Blowing Insights About Hardware-Backed Authentication That Will Change How You Think About Cloud Security
We've all been there; another leaked API key, another compromised credential, another midnight emergency call. The traditional approach to cloud security—rotating passwords, managing access keys, praying nobody commits secrets to GitHub—feels like fighting a losing battle. -
The Password Crisis Nobody Talks About: 5 Surprising Lessons from Hardware-Rooted Cloud Security
We've all been there - juggling AWS access keys, rotating credentials quarterly, and praying that developer laptop that went missing last month didn't have plaintext keys. The conventional wisdom says "use long, complex passwords" and "rotate regularly." But what if the real solution is to eliminate passwords entirely? -
Righty Tighty: The "Physics-Compliant" Approach to Cross-Cloud Security
We’ve all been there - juggling long-lived AWS access keys, managing OCI config files, and praying that the "secret" API token committed to a private repo three years ago doesn't come back to haunt us. But what if we treated cloud identity less like a password and more like a physical law? -
Your Security Agent Isn’t Broken—It’s Just Optimizing the Wrong Universe
We've spent decades perfecting code correctness—yet some of the costliest failures come from agents doing exactly what we told them to do.
November
-
7 Ways zk-Autograd Reimagines Trust in AI Training (One Gradient Step at a Time)
We talk about “trusting” AI models, but almost no one can prove how they were actually trained. zk-Autograd treats every gradient step like a cryptographic contract. -
Why Your Next Security Architecture Should Be Ephemeral (and Why We Built It That Way)
We built a signing service that doesn't trust its own keys. Here's why that's the future of security.
April
-
7 Ways Mimir Makes LLMs Safe Enough for People Who Don’t Trust Each Other
In most LLM systems, someone has to trust someone else with raw prompts or weights. Mimir shows what happens when nobody is willing to blink. -
How This Architecture Is Defined By the Next Decade of Security
Today’s security tools were built for a world of static infrastructure, predictable threat models, and manual operations. But that world is gone. -
GPU Budgets, Global Models, and Real-Time Risk Scoring Infra Deep Dive
It’s one thing to train a model in a notebook. It’s another to scale that model across multiple clouds, regions, and time zones—scoring millions of events in near-real-time. Energy-Based Models give you power. But that power has a price - compute, latency, and orchestration at scale. -
⚖️ Can You Trust an AI to Contain a Threat? Legal and Privacy Teams Say Maybe
the moment you say “no human in the loop,” the room changes. “Who’s accountable if something goes wrong?” “How do we prove what happened during an audit?” “Can this system violate a user’s privacy policy?” These aren’t just hypothetical questions—they’re the frontline concerns of your legal, privacy, and compliance stakeholders. And if they’re not addressed head-on, your autonomous response system will never see production. -
🧬 From Static Rules to Self-Improving Response Playbooks
We’ve all seen it. A detection fires, but the response is ineffective. An alert escalates to the wrong channel. A playbook quarantines the wrong asset. Or worse—nothing happens because the logic broke after a cloud migration. Why? Because traditional playbooks are manually written, rarely tested end-to-end, and drift out of sync with reality. But what if they could test themselves? Better yet what if they could optimize themselves? -
No Schema? No Problem. Let AI Handle Your Security Data Onboarding
Data is messy. Engineers are busy. And yet, every new application or microservice adds more logs that need to be parsed, structured, and made useful. This used to be a blocker. Not anymore. For years, one of the hidden pain points in detection engineering has been log ingestion and normalization. Most SOC teams rely on detection rules that assume data shows up in a clean, consistent format. -
🔁 Build Once. Learn Always. Inside the Autonomous Detection & Response Loop
Let’s be honest—static playbooks aren’t enough anymore. You can’t write a workflow for every edge case. Threats change. Your infrastructure changes. And every incident teaches you something that gets lost in the backlog. But what if your detection and response system actually learned from every incident? -
⚡ What Makes Energy-Based Models So Effective for Anomaly Detection?
Traditional detection systems—rules, heuristics, even many ML classifiers—struggle in this gray zone. But energy-based models were built for it. -
🧱 Why Security Operations Can’t Scale Without Automation
Security operations centers were never meant to scale like this. What began as centralized log review has ballooned into an arms race of dashboards, SIEM queries, and tier-1 analysts buried in alert queues. Meanwhile, attackers have automated everything from lateral movement to domain privilege escalation.
2023
December
-
Embracing the Cyber Age- The Art of Adaptability in Security Engineering
In the dynamic and ever-evolving realm of digital technology, the need for adaptability in combating cyber threats has never been more pronounced.
November
-
Securing the Digital Frontier- The Essential Role of Education in Tech Literacy and Security Awareness
In the rapidly evolving digital landscape, where technology deeply permeates every facet of our lives, the importance of tech literacy and security awareness cannot be overstressed. -
The Tightrope Walk- Balancing Security Engineering and Privacy in the Tech World
In the rapidly evolving world of technology, a critical and often controversial issue stands at the forefront the balance between robust security measures and the protection of individual privacy rights. -
Embracing Decentralization- The Future of Democratic Oversight and Security Engineering
In an era where digital technology is not just a tool but a societal cornerstone, the concepts of democratic oversight in technology and decentralized security models in security engineering are more relevant than ever. -
Annabel's Cypherpunk Manifesto
It was many and many a year ago, In a realm of digital glow, That the Cypherpunks came to know, A love for privacy, like a river's flow.
March
-
2023 update to 2021 White House Cybersecurity Executive Order
I realized I needed to update the 2021 White House Executive Order …Improving the Nation’s Cybersecurity fundamentals outline. In order to scale with limited resources to achieve the basics, below are the fundamental hygienic basics one must achieve.
February
-
Striking the Right Balance- Innovation and Regulation in Security Engineering
In the fast-paced world of technological advancement, balancing innovation with regulation is a crucial challenge, especially in the field of security engineering.
2020
December
-
Intel Sharing Metrics
I pulled some metrics from my threat intelligence sharing service to generate cute charts and graphs. If you want to keep up to date, keep an eye on
February
-
Failure to meet operational excellence
One would think to rotate their certificates months prior to expiration. Or even the bare minimum
2019
November
September
-
Kubernetes CI / CD And Monitoring Pipelines
When one takes a step back and looks at a typical agile build, test, and release pipeline with a security bent; one observes the following steps and how they feed into each other like a dragon eating its’ tail.
July
-
Kubernetes Pods (PodSec policies)
Pods hardening is strongly configured and enforced with Pod Security policies (PodSec.). The security context enables not to restrict privileges, volume mounts, network privileges, cgroups / selinux / app armor / kernel capabilities, access control, read only file-system, etc…. This is where much of the workload insecurity comes from. -
Kubernetes Containers
When we get into the specifics for containers, the challenge is that the detailed advice differs greatly between the different container technologies. As a result, I will STRONGLY recommend one doesn’t run Docker as it was never designed to be secure, requires Swarm to manage some aspects of its’ lacking security, and requires a near-infinite amount of hand holding -
Kubernetes Networks - CNI
Within Kubernetes, networks are an interesting beast. They become extremely muddled -
Kubernetes Master Node & Nodes
One will wish to replicate their Master node to minimize downtime events. These nodes will host the control plane building blocks -
Kubernetes Scheduler
Overview
-
Kubernetes Information Security Practices
We sponsored a Kubernetes security review because of its’ popular adoption, glaring insecurities, default insecure states, wasn’t designed to be secure, and everyone wanted to use it and make it available to the Internet -
What is a modern, dynamic service and its' building blocks?
As I work through the ecosystem, there is no evident, leading best practice. -
Nginx exploit writing weekend
This weekend will be ripe of opportunities for nginx exploit writing. Trying a new scheduler algorithm and Stensal's compiler against nginx's stable code base. -
Kubernetes Basics
Let’s take a look at the simplest part of the previously documented multi-tenancy architecture
June
-
What does it take to break into a Cloud Service?
Sometimes, all it takes is cp and rsync. See the image below for an example.
March
-
When your SIEM models are not enough
Just when I thought every bit of value was squeezed from the systems, it is continuing to pull out indicators and APT actors like candy at a weight loss camp.
January
-
OSX First Responder - Threat Artifact Gathering
How you go about hunting down malware on a macOS endpoint depends a great deal on what access you have to the device and
2018
November
-
Memory Safety Code Review
Some of our keen readers may have noticed that if the size of userPass is less than 9, then overflow will still occur.
September
-
Solving 90% of application security defects with a proven technique
Even when validation is used, a common mistake is to use block lists. For example an application will prevent symbols that are known to cause trouble. The weakness of this countermeasure is that some symbols may be overlooked. -
Data Controls Code Review
The number of user records exposed in the United States has been in the billions in 2016 and 2017. 2018 will likely be the same, once the final tally is calculated. -
Binding Parameters
Notice that the single quote in the name O’Brien is causing a syntax error. The SQL command processor considers the string ends -
Overly Simplistic Crypto Code review
Confidentiality is one of Information Security
July
-
For those who wonder what a Digital authentication cyber arms race looks like
It is heavy on the technical content but is entertaining if you spend the time understanding the language.
April
-
First 100 Days
A friend took up a new InfoSec executive career path but didn't know how to start. She reached out to me and ask for my thoughts. I thought about it
January
-
The pending crypto singularity
Recently penned by Peter, it is worth a read. Especially for those who are concerned about putting all of their eggs in one basket. On the Impending Crypto Monoculture
2017
October
-
Creating a Loki Splunk application
One tool that has caught my interest is the [Loki APT scanner
September
-
Serious XSS affecting Wikipedia
XSS vulnerability in thumb.php in Wikipedia Mediawiki -
Defense Against the Dark Arts
Thankfully, Naurus has produced a useful infographic to understand the variety of malicious entities. While it is not all inclusive, it suffices to help one quickly prototype simple threat models.
April
-
Walking the Dark Deep Web
During Black Hat, BsidesLV, and Defcon, I ended up having a chat with Justin Seitz about his nifty OSINT automation. I decided to take his data sets and enrich
2016
August
-
DARPA Cyber Grand Challenge era coming to a close
This Thursday, seven research institutions will compete against each other. Unlike other typical hacker challenges, their automations will compete on their behalf. The winning team will take home
March
-
Multiple vulnerabilities in SecurityOnion
Let this be a reminder of the joys in programming PHP -
Relatively Free
From my text library, this is list of software
February
-
Ransomware hitting linux hosting providers
It will be interesting to watch the infection spread on Google Trends
2015
November
-
DARPA Cyber Grand Challenge dropbox
I have been taking lessons learned from DARPA’s Cyber Grand Challenge and applying it to our automation
August
-
Hotpatch Redis's RCE
Do you feel lucky
July
-
Ingenious CTF dashboard
As taken from a dummy account, I wish more CTFs were setup like this. [#Polictf](https://twitter.com/search?q=%23Polictf) 2015 -
Destroy a City - secure code review
It should be noted that no ethically-trained software engineer would ever consent to write a DestroyBaghdad procedure
June
-
Social Engineering Confirmation Bias workflow
The image below shows the role confirmatory bias can play in social engineering exploits. Two situations are depicted. In the first, the insider desires access to information supplied by the -
Redis RCE
If you haven't already, time to patch Redis. Otherwise, please setup authentication in front of your Redis instance. This remote code execution is going to get nasty http -
ElasticSearch honeypot dataset
I have uploaded a new ElasticSearch honeypot dataset. It appears there are a few individuals who are attempting to exploit a few 0days in ElasticSearch. All the more reason not
May
-
Ghcq Challenge Completed
View fullsize
April
-
Impressive Node.JS vulnerability reduction
In 2013, when I last performed a secure code review on Node.JS, it did not look pretty. -
Need help figuring out a Snapchat username? I have your back.
I can’t tell you what makes a good Snapchat username. But what I can tell you is what makes a popular Snapchat username. -
Yet another nail in SSL TLS 's coffin
RC4 has long been considered problematic, but until very recently there was no known way to exploit the weaknesses -
Technical Approaches to Determining if an Incident Occurred
When addressing potential incidents and applying best practice incident response procedures
March
-
Open Source Fairy Dust Datasets
The current list of open source critical infrastructure services vulnerability metrics I have released and / or made public -
Checkbox AWS assurance testing?
A great beta tool to checkbox their AWS infrastructure and account to known AWS controls. [ Scout2
2014
December
-
LDAP Tool Box vulnerabilities
This vulnerability allows one to bypass weak XSS filtering
June
-
How to sell a story - Ira Glass
If you are just starting this phase, still in this phase, getting out of this phase, you gotta know
April
-
Please donate to a worthy crypto security cause
If you have ever used OpenSSL, [please donate money to this worthy cause -
Bug Age - Pattern series
I love standards. My blackhat persona says this makes it easy to break into systems
March
-
Chrome's V8 double free vulnerability
Within Chrome's V8 engine, this was an interesting double free vulnerability I uncovered. Thank you V8 team for accepting.
2013
November
-
NodeJS vulnerabilities - it hurts to look
Background
July
-
Google Translate
the translated website pops out of Google Translate's iframe and redirects the user to a website or content of their choosing
June
-
Random thought for an exploding honey token
I remember when Nuxi and I would create computationally compact compressed files and see which mail servers would attempt to inspect the contents. Typically, the MTA would fail over due -
Carberp Vulnerabilities Cc Pie
I logged into Reddit this morning and observed Carberp -
Apache Batik parse double vulnerability
It is interesting to see Batik's parse double vulnerability exist to this day. Anyone want to crash Opera or popular, open source software -
DAQ buffer overflows
Sourcefire and snort vulnerabilities allow remote code execution -
Malicious mobile power station
A bit back, I looked over Stavrou USB smartphone paper evil power station -
Startup Comp Structure
You -
Lazy AWS devops
I am seeing too much echo chamber, saber rattling, foolish dogma about agile SA
May
-
Security is hard. Security Tools are harder. Cloud Security Tools are hardest.
There are tools, security tools, and then there are cloud security tools. Especially in the realm of security orchestration. Many cloud snake oil tools were never designed for the cloud. -
CNN.com XSS vulnerabilities
CNN fixed two XSS issues. Congrats -
Google Glass Developer program - more DOS and XSS
There were two very simple Google Glass Mirror's quickstart DOS and XSS vulnerabilities. The fixes have been introduced in changeset https
April
-
Google Glass 0days
Jenny Murphy has some clean code. However, it isn't the most secure. The Google Glass team must be under an intense timeline. Without looking too hard into the libraries and -
Evolutionary hardware
For technical problems, one may struggle to define the specifications. When this happens, look at the behavioral design. Then one may find solutions from the design automation. Thankfully, evolution algorithms -
Rapid7 Google hacks extended
How many other file sharing services are affected by the inadvertant sharing of sensitive information
2012
December
-
Nifty Anti-XSS validation tool - Snuck
To significantly test a given XSS filter by specializing
October
-
Firesale WebPanel botnet 0days
Oh, Firesale WebPanel botnet. How entertaining it is to see you continue to raise your head over the years.... XSS Reflected -
ERM - How did WOPR decide the only winning move is not to play?
WOPR evolved and learned while playing against himself
September
-
DPAPI still applicable?
I saw some code utilizing DPAPI. Given the research around MS's poor DPAPI implementation,
August
-
Security quotes
The present need for security products far exceeds the number of individuals capable of designing secure systems
July
-
Management Wednesday- BPM Modeling - not charts anymore
After one has accomplished the scoping phase, then the team should move on to modeling. Due to the large amount of time spent scoping, many scenarios will come to light
June
-
Microsoft revokes Microsoft's certificate
It is a sad day when a PKI private key signing software is able to sign code on behalf of Microsoft. Especially when it is found in the wild and
May
-
Gribodemon on SpyEye 2.x - I expected better
Saturday, I noticed my application honeypot collected an interesting sample. The cracker took my bait and attempt to hack the planet via a SpyEye 2.x variant. Apparently, the limit of -
Airing one's dirty development laundry - You are doing it wrong
I recieved a lovely google alert this weekend. -
Bitcoins are hard to track
Either FBI -
Sad reality
hope you have a gating process in your finance team which halts the ability to pay vendors without security approval... -
Management Wednesday- BPM scoping
In business process management, there is no defined starting point. The solutions are transposable, adaptive, and can be set into motion regardless of the other solution's state. In project's scoping -
PHP - two simple wins and a hammer
I love programming in PHP. Fairly simple to learn, easy to code, plenty of tools available, and great community. However, due to the language's inherent behaviour, PHP has many security pitfalls. -
Meltdown exploits
Here is an academic exercise to create the Meltdown exploit prior to publication on Jan. 9th. To keep honest with my CISSP certification, I didn't include all operating systems and
April
-
Management Wednesday- BPM isn’t beats per minute.
I was chatting with Alexander Peters and he mentioned an interesting statistic. -
Management Wednesday - Negotation
Management 101 - Negotiating Observe yourself negotiating The more time one spends preparing is directly related to win
2011
April
-
Web Application Security Dojo 'grams
While finding innovative methods to visualize various web application insecurity practices, I came across a great visual aid. Enjoy. Credit